I’ve been involved in a few international projects where we used a Cisco 819 router to handle a small network, using a broadband connection as the primary connection to the Internet, and the built in cellular connection as the backup. I thought I’d talk about the basic config for this, some options you have with the cellular backup configuration, and other things I noticed in working on these projects that were notable.
The hardware
First things first, if you are planning on deploying one of these, make sure you order the right hardware. There is a different model depending on which type of cellular technology your carrier supports.Check out this Cisco link and look at Table 2. There are three models you have to choose from:
- C819(H)G-4G-V-K9 – Works with Verizon networks, hence the “V” in the product sku
- C819(H)G-4G-A-K9 – Works with ATT networks, hence the “A” in the product sku
- C819(H)G-4G-G-K9 – Works everywhere else, “G” for global in the sku
The (H) in parenthesis is optional depending if you require a hardened version of the hardware for harsh environments.
Pick your carrier
If you’re trying to install this in a location you aren’t familiar with it can be hard to determine who the best cell carriers in that area are. I found this great website www.opensignal.com that collects and pools data from droid and iphone device apps to determine signal strength and performance across the globe. You can type in a location to search and it will show you both the top carriers in that area and coverage on a map. If you check this page out you can get a list of every country they have data for, the top available carriers in that country, and clicking any carrier will give you a coverage map and statistics on performance like download/upload speeds and latency.
Get your SIM Card
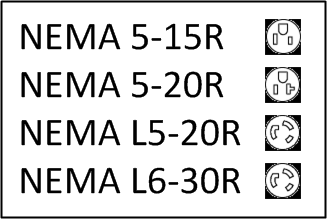
After you have the hardware you will need to place an order with your cell carrier for the SIM card. SIM Cards come in different sizes, as seen in this wikipedia article. The Cisco 819 supports the Mini SIM (Size 2FF). I think I read in one of the support docs that you could use a Micro SIM( Size 3FF) if you had an adapter, but I didn’t test it out, and just decided to use the default supported size.When you order your SIM card you should ask your carrier what the APN(Access Point Name) you should be using is. When your cellular router makes a connection to the mobile network it will present an APN which will help determine the type of network connection that will be created. This varies per carrier so you’ll just need to ask your sales or technical team for that info. Also keep in mind how much data you might be sending over this connection when sizing your plan. Overages in cellular data use can get expensive very quickly so order appropriately. Some carriers offer M2M plans which allow you to share data allowances between SIM cards which becomes very useful if you have a large number of sites using this technology as a backup. Going with this type of deployment you could get away with a small data cap, inexpensive monthly plan of some number of megabytes per site, which will mostly go unused(hopefully if your primary connection is reliable), but when it does need to be used at any one site you’ll have the power of that pool of data allowances to tap into(for example maybe each site is 25MB per month but you have 100 sites, that gives you 2.5GB total to use).
Router Config
As mentioned in the intro, my config will use broadband as the primary connection and cellular as the backup. I’ll show two different options for the cellular backup as well: Triggered/dialing on demand and always on.
Triggered Cellular Backup
In this design traffic will get sent to the broadband connection under normal circumstances and will get sent towards the cellular interface if there is a problem with the broadband. In order to add a little bit of intelligence to detecting when there is an issue with the broadband connection we’ll use a combination of IP SLA and tracking to ping a host (Google’s Public DNS 8.8.8.8 in this example, although I would not recommend you use that in production since you have no control over Google’s uptime, may be better to test pinging the default gateway of the Broadband provider instead).
To start off we need to create a cellular data profile on the router. This contains information such as the APN, authentication type, and username/password if applicable. All of this info will come from your provider. To create the profile you’ll enter something like this:
router#cellular 0 lte profile create 1 <APN_GOES_HERE> pap <USERNAME_HERE> <PASSWORD_HERE>
After you create the profile we can continue with the config. This is how the config will work:
- Traffic normally is NATTED and sent out the Gi0 broadband interface to the internet. This is sent to the Gi0 interface using a default route with a track object on it. An IP SLA check is running over the Gi0 interface as well, testing ICMP to 8.8.8.8.
- If the IP SLA object fails,the track on the default route towards the Gi0 interface will cause that default route to be removed, leaving a second default route that points towards the cellular interface, but had a higher admin distance(so wasn’t used).
- Once any IP traffic is detected by the dialer list, it will cause the chat script referenced under the cell0 interface to run the ATDT commands and dial the modem.
- The modem will start and establish a cellular connection. This connection will stay up as long as there is traffic detected. If there is no traffic detected in the idle timeout(currently set at a default, can be modified under the cell0 interface using dialer idle-time), the connection will go down. This is good in that it helps conserve data usage costs for your cellular.
- In the background, the IP SLA traffic is still trying to reach 8.8.8.8 via the Gi0 interface. Once the IP SLA is successful, the original default route will go back into effect, and traffic will start going out the Gi0 interface again.
chat-script lte “” “AT!CALL1” TIMEOUT 60 “OK” !Chat script called ‘lte’ used to dial the modem with ATDT commands
ip sla auto discovery
ip local policy route-map sla-route !Local policy for traffic originating from the router going to 8.8.8.8 over the Gi0 interface (which is set using the route-map sla-route)
ip sla 100
icmp-echo 8.8.8.8 source-interface GigabitEthernet0 !IP SLA ICMP test to 8.8.8.8 sourced from Gig0
frequency 10
ip sla schedule 100 life forever start-time now
track 100 ip sla 100 reachability !Tracking object that is tracking the state of IP SLA object 100
delay down 10 up 20
dialer-list 1 protocol ip permit !Dialer list that defines what traffic is allowed to start the cellular connection.In this case any IP traffic will trigger the connection.
ip dhcp pool testpool !DHCP Pool for clients
network 192.168.0.0 255.255.255.0
default-router 192.168.0.1
dns-server <DNS_1> <DNS_2>
!
interface GigabitEthernet0
description Broadband Connection
ip address <Broadband_IP> <Broadband)Mask>
ip nat outside !Outside interface
duplex auto
speed auto
!
!
vlan 10
interface Vlan10
ip address 192.168.0.1 255.255.255.0
ip nat inside !Inside NAT Interface
ip virtual-reassembly in
interface Cellular0
ip address negotiated
ip nat outside !Outside interface of NAT
ip virtual-reassembly in
encapsulation slip
ip tcp adjust-mss 1000
dialer in-band
dialer string lte !The chat script to use when dialing the cellular interface. This needs to reference the same name you used in the chat script of the first line of this config.
dialer-group 1 !This is tied to the dialer-list 1, which defined what type of traffic should trigger the cellular connection
async mode interactive
ip nat inside source route-map wan-backup interface Cellular0 overload !NAT statement used for cellular
ip nat inside source route-map wan-primary interface GigabitEthernet0 overload !NAT statement used for DSL
ip route 0.0.0.0 0.0.0.0 <Broadband_Default_Gateway> track 100 !Main default static route pointing towards the DSL, with tracking
ip route 0.0.0.0 0.0.0.0 Cellular0 10!Second default route for secondary connection(Cellular), with a higher AD. This will only get installed in the routing table if the primary route gets removed.
access-list 100 permit ip 192.168.0.0 0.0.0.255 any !NAT ACL, NAT anything with a 192.168.0.x IP address, which is all PDQs
!
route-map sla-route permit 10 !This is a special route-map to make sure the IP SLA traffic goes out the Gi0 interface and not the cellular.
match ip address sla-packets !Match the ACL for sla packets
set ip next-hop <Broadband_Default_Gateway> !This is important. We want the SLA traffic to always be routed out the broadband interface so we have a true indication of when there is an issue with the broadband. if we don’t specify the next hop the SLA traffic will bounce between broadband and cellular as they go up/down, and will constantly change states.
set interface Null0
!
route-map wan-primary permit 10 !Route map used to define the source IP addresses when on DSL
match ip address 100
match interface GigabitEthernet0
!
route-map wan-backup permit 10!Route map used to define the source IP addresses when on cellular
match ip address 100
match interface Cellular0
!This EEM applet came up after testing this and have it not work perfectly. What I saw happening was when the connection failed over the old NAT entries were still pointed towards the previous interface(broadband – when it failed over to cell) causing traffic to not flow correctly. This EEM applet looks for the Tracking state to change and then clears the existing NAT translations, which allows them to be rebuilt using the new cellular outside IP. I’d be interested in hearing how other people have handled this without using the applet.
event manager session cli username “admin”
event manager applet CLEAR_NAT
event syslog pattern “TRACKING-5-STATE”
action 1 cli command “enable”
action 2 cli command “clear ip nat translation forced”
action 3 cli command “exit”
Always-on Cellular Backup
If you prefer the cellular connection to stay on all the time then you can make these changes to the above config:
Router#config t
Router(config)#int cell 0
Router(config-if)#no dialer-group 1 !Remove the dialer-group 1
Router(config-if)#dialer watch-group 1 !Add a dialer watch-group
Router(config-if)#exit
Router(config)#no dialer-list 1 protocol ip permit !Remove the dialer list
Router(config)# dialer watch-list 1 ip 5.6.7.8 0.0.0.0 !This is a fake IP the router uses to generate traffic and keep the interface up.
Router(config)# dialer watch-list 1 delay route-check initial 60
Router(config)# dialer watch-list 1 delay connect 1
!With the configuration above this point, the cellular would stay up all the time(even with broadband up). These EEM applets will follow the state of the tracking object and perform a ‘shutdown’ of the cell0 interface if the track is ‘UP’ (broadband working), and will perform a ‘no shut’ on the cell0 interface if the track is ‘DOWN’ (broadband down).
event manager applet Cellular_Activate
event track 100 state down
action 1.0 cli command “enable”
action 1.1 cli command “configure terminal”
action 1.2 cli command “interface Cellular0”
action 1.3 cli command “no shutdown”
action 1.4 cli command “end”
!
event manager applet Cellular_Deactivate
event track 100 state up
action 1.0 cli command “enable”
action 1.1 cli command “configure terminal”
action 1.2 cli command “interface Cellular0”
action 1.3 cli command “shutdown”
action 1.4 cli command “end”
Wrapup
Hopefully this was a good overview of how to configure one of the Cisco cellular routers. There are other ways you could approach the primary/backup configuration, this was just one config I had come up with that gets the job done. What type of cellular configs are you using?